Security of smart contracts written in the Solidity programming language
Software Computing
Coding smart contracts in the Solidity programming language represents a special challenge, as the specifics of blockchain technology require the use of unconventional programming patterns.
Any bugs and security flaws written in the code are visible to everyone, as the source code of smart contracts is publicly viewable. From the security point of view, it is therefore recommended that the Solidity programmer should have a good knowledge of established programming design patterns.
That allows him or her to write functional programming code and reduces the possibility of making mistakes.
In our thesis, we discuss the difference between different types of distributed consensus algorithms and list the basic building blocks of blockchains.
By listing concrete examples of blockchain use in real business situations, we wanted to showcase that smart contracts are not only used in the field of financial transactions.
Further, we deal with the specific characteristics of the Solidity programming language and define its strengths and weaknesses.
As one of the major weaknesses of Solidity, we can certainly point out its young age, as well as the relatively large number of security flaws, frequent changes, and upgrades of the program Solidity programming language.
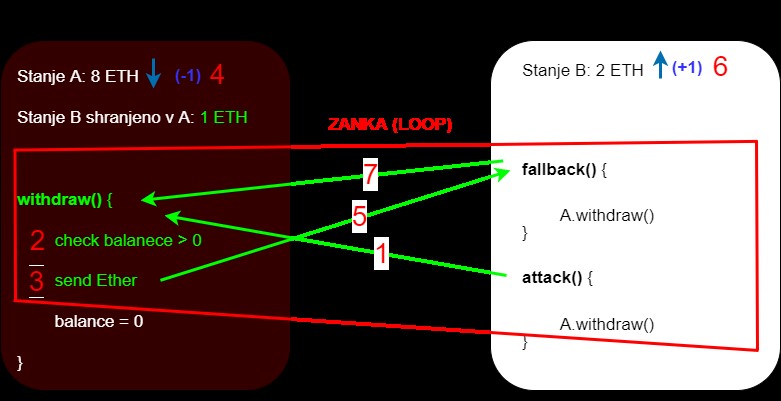
For this reason, we listed the most significant and most common vulnerabilities of smart contracts written in the Solidity programming language.
For each described vulnerability, we quoted an example and provided recommendations on how to avoid or at least reduce these vulnerabilities. Where possible we provided also examples of vulnerable code and code where we tried to fix the quoted vulnerability.
Based on the listed vulnerabilities and given recommendations, we prepared a checklist, which could serve as a quick reference for programmers when coding smart contracts. For further simplification of the checklist usage for each vulnerability, we provided a field, to which it relates to.
For that reason, we also included a brief statement regarding recommended and discouraged practices in the checklist.
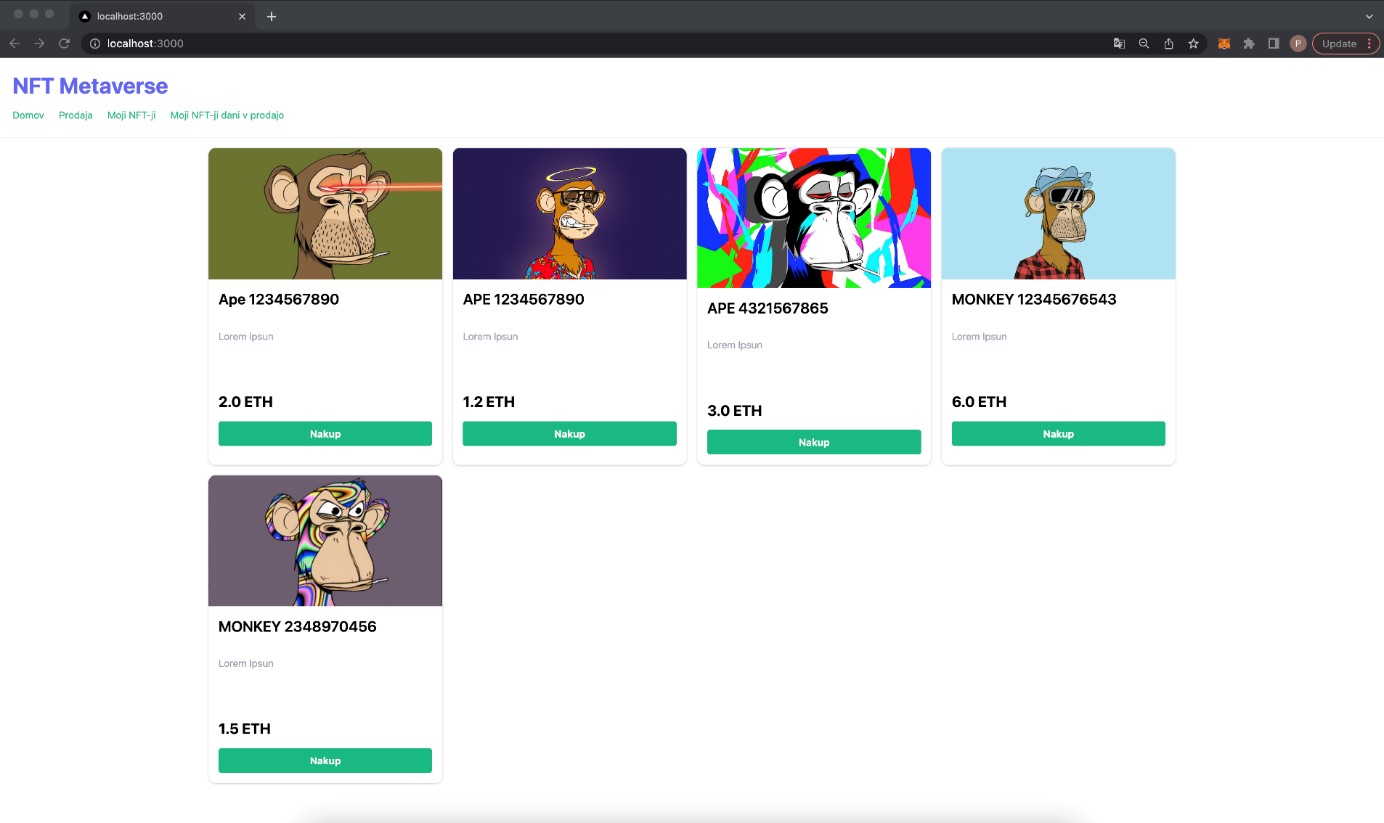
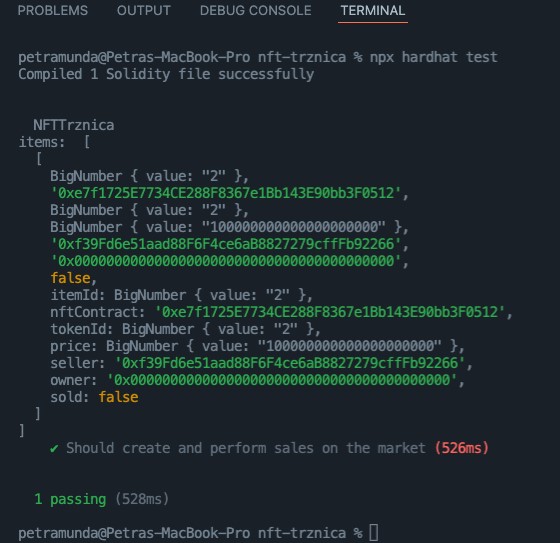
We then incorporated that knowledge into writing our own example application, an NFT token marketplace, allowing the users to connect their wallets and sell their tokens.
The application consists of two smart contracts and a simple graphical user interface written in JavaScript.